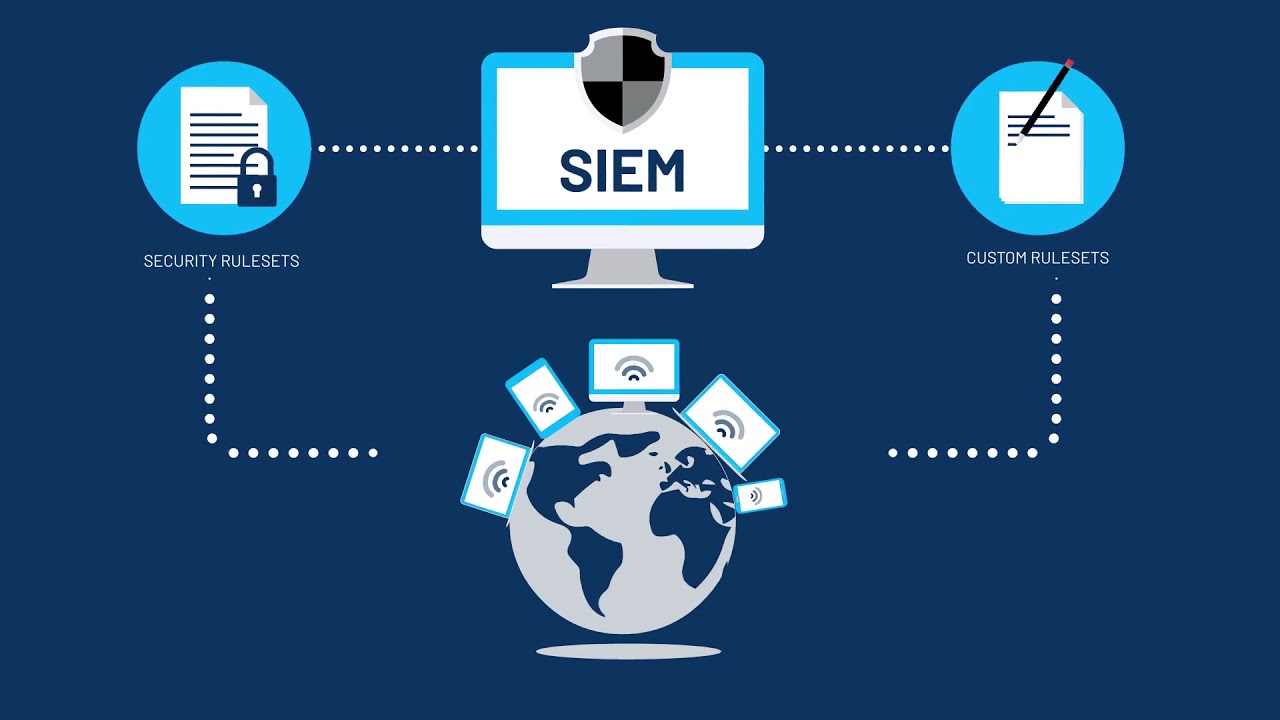
If you’ve never heard of this software, your first question may be ‘what does SIEM stand for?’. The SIEM abbreviation stands for Security Information and Event Management. SIEM is defined as a software solution that manages various activities throughout your entire infrastructure. And with Klik Solutions as your managed IT services provider, your system will always be held to the highest cyber security SIEM standards. Klik these links to learn more about our managed IT services and IT security services.
What is SIEM Technology
This software solution uses an analysis, alert, and reporting system as a security measure for your company’s infrastructure. SIEM alerts can be about various system aspects. Here are some of the things your IT provider should be looking out for:
- Acceptable Use Policy Violations. Let’s be honest, employees hardly ever read the AUP’s, or Acceptable Use Policies. Because of this, these procedures are rarely followed. Monitoring AUP violations will allow you to find the exact end-user with installed malware.
- Account Management & User Privilege. Monitoring these alerts will help your provider decrease the chances of malware getting into your infrastructure through end-user endpoints.
- Abnormal External Communication. By following suspicious extrinsic communication alerts, your provider will have the resources they need to filter, manage, and intercept these out-of-the-ordinary external communications.
- Unusual Port Activity & Data Exfiltration. When ATP’s, or Advanced Persistent Threats, rear their ugly heads, data exfiltration is the main target. By tracking port activity alerts your security team will know the right time to check backdoors, applications, FTP’s, and Window Management Instrumentation for irregularities.
- File Integrity Monitoring. Keeping a close eye on your file activity will allow your tech to integrate file access auditing. This auditing service enables them to see if files have been tampered with, created, or erased.
Most Used SIEM Tools
For your leisure, we’ve listed the top SIEM utilities used today:
- IBM QRadar. A well-known software solution that can be used on multiple machines and platforms. Such as hardware, software, and virtual. The optimization depends solely on your business’ needs
- Splunk. A solution that enhances security measures while offering optimal threat detection.
- LogRhythm. This product is best for small organizations. It works by offering system threat discovery and resolution competency.
Why SIEM Reporting is Crucial for Securing your Network
This software solution has so many benefits, but the main benefit of this is its ability to make security filtering easier for big organizations through mass data filtration. It’s a hacker’s job to make their threats virtually undetectable. Luckily, SIEM allows IT technicians to detect and treat these threats while preventing damage increases. Thanks to the mass data logging this software promotes, organizations can branch out and increase their data usage.
Not only does SIEM help with cybersecurity, but it also helps with compliance upkeep. By creating automated service reports, this software enables your IT provider to have perpetual security logs.
Another benefit of this software is its ability to manage incidents by giving technicians the tools they need to pinpoint the source of an attack, find the affected sources, and prevent future attacks of the same nature.
Here at Klik Solutions, we always want to make sure all of your cybersecurity and compliance needs are met. If you have any questions about our SIEM processes or want to see how we can benefit your company just give us a call at (888) 959-1196 or Klik here to visit our website and schedule a consultation